Which platforms, languages and formats are supported?
Android (APK and AAB), iOS (IPA, including FairPlay-encrypted via on-device runtime), web apps and APIs, and source repositories in Kotlin, Java, Swift, Objective-C, JavaScript, TypeScript, Python, Go, PHP and Ruby. SAST, DAST and SCA in one scan.
My app ships on both iOS and Android. Is that one subscription or two?
One. Every paid plan includes unlimited apps across platforms. We never charge per-app or per-platform on the public tiers.
How long does a scan take?
A typical SAST run finishes in under 5 minutes on a mobile app. DAST on a real device takes 10 to 25 minutes depending on UI depth. Web URL scans depend on target size.
Do you store my source code or binaries? For how long?
Hosted entirely in the EU (Germany). Uploads and intermediate artefacts auto-delete according to your plan's retention. You can also delete a scan and all associated data at any time from the dashboard.
TitanShield Intelligence: how do you handle fixes you can't safely automate?
TitanShield Intelligence is our autofix engine. When a fix is safe and isolated (outdated crypto, missing flag, hardcoded secret), Intelligence opens a pull request directly on your repo with the patch and unit-test proof. When a fix is sensitive (auth flows, business logic, anything that could regress in production), we never push code we are not 100% sure about. Intelligence ships an expert fix guide your engineers apply with their context. Our promise: we never break your production.
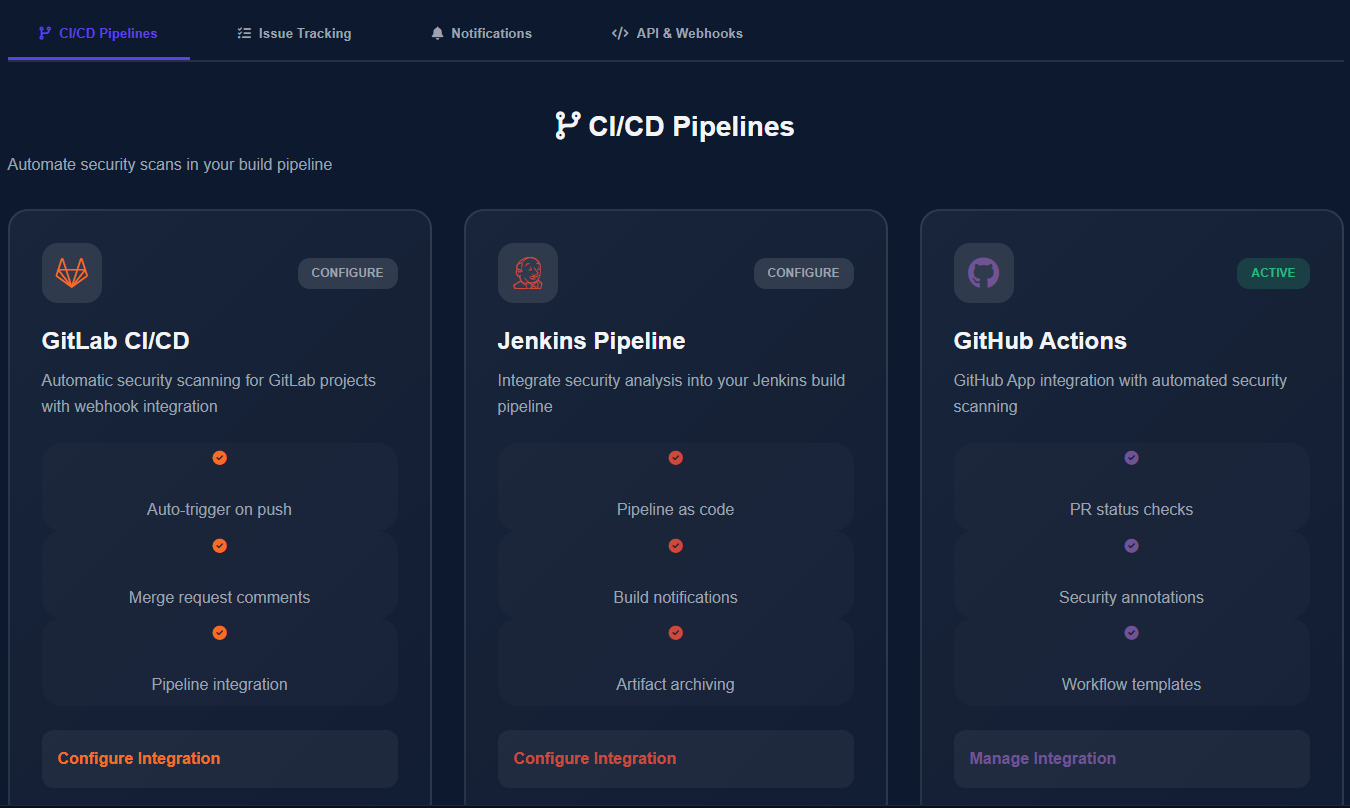
Which CI/CD systems do you integrate with?
GitHub Actions, GitLab CI, Bitbucket Pipelines, Jenkins, CircleCI, Azure DevOps and Bitrise are wired natively. SARIF export covers any other runner. Findings can ticket to Jira and notify Slack.
How is this different from MobSF or other open-source scanners?
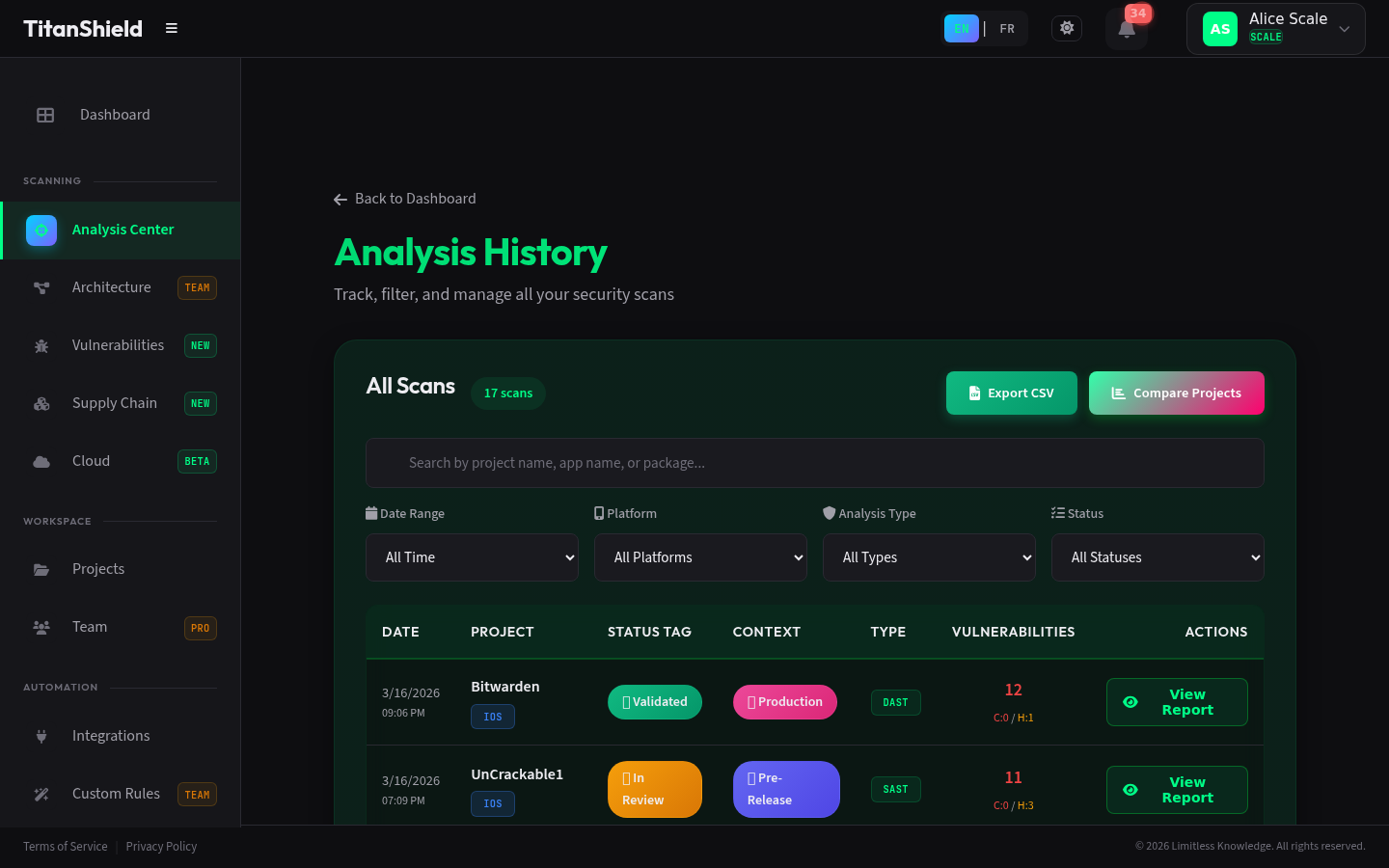
Open-source scanners give you raw findings. We add ML false-positive filtering (about 80% fewer noise findings on a Bitwarden benchmark, 56 down to 11), open a pull request with the fix when possible, and run everything in the EU with no third-party AI dependency.
Why TitanShield instead of an established AppSec vendor?
Most appsec platforms ship findings; we ship the patch. Four differentiators: EU sovereign by design (every byte of code, every AI call and every artefact stays in the EU on our own infrastructure, no US cloud, no third-party AI APIs); the autofix PR is the moat (not a report, an actual code patch on your branch); native CI/CD across 7 systems plus SARIF, no agent to install; flat predictable pricing, self-serve from day one, no enterprise contract required to start.
Do I need a credit card to try TitanShield?
No. The Community plan is free forever and lets you run real scans. A card is only required when you upgrade to a paid plan.
How do I cancel? Is there a refund?
Cancel any time from the billing page. Within the first 14 days, cancelling triggers a full automatic refund. After that, you keep access until the end of the billing period.
How do team workspaces and seats work?
Team workspaces with multiple users are in private beta on Business and Enterprise plans. The architecture is built around organizations: scans, billing and audit trail live at the org level, and members can belong to multiple orgs. Talk to us to onboard your team early.
Is on-premise deployment available?
Yes, on the Enterprise plan. Air-gapped install on your own infrastructure, with a dedicated upgrade channel and SLA. Get in touch to scope it.